D-FORTRESS: Unbreachable Data Survival Structure.
PZT-Vault: A Ransomware Defense-Specialized Backup System based on Physical Zero Trust (PZT) Architecture.
Request Demo & Consultation Explore Key TechnologyRansomware attacks are no longer just about encrypting files; they aim to destroy the backup system itself. Is your backup truly safe?
Most 'Air-Gap' solutions rely on software-based, logical isolation. If a hacker infiltrates the system with administrator privileges, they can reactivate this logical connection, accessing or deleting backup data.
Once an attacker steals administrator credentials or escalates their privileges, all security policies are nullified. Accessing the backup server's OS allows for data deletion and system format.
Malicious insiders or accidental operator errors can compromise the backup system. Every person and every path with access to the system becomes a potential threat.
PZT-Vault implements a Physical Zero Trust environment that ransomware can never access.
By utilizing a **Data Diode**, data flow is permitted unidirectionally from the backup server to the storage, while communication in the reverse direction (from storage to backup server) is fundamentally blocked. This establishes a **physical, one-way security channel** that is uncontrollable by software, completely isolating backup data from external threats.
Once written, backup data is preserved in an absolutely unchangeable, undeletable, and unencryptable state for the configured retention period. Even administrator privileges cannot alter the data.
Physical connection is only permitted during data recovery, a process that follows strict multi-factor authentication and rigorous protocols. The recovery environment itself is completely isolated from external threats.
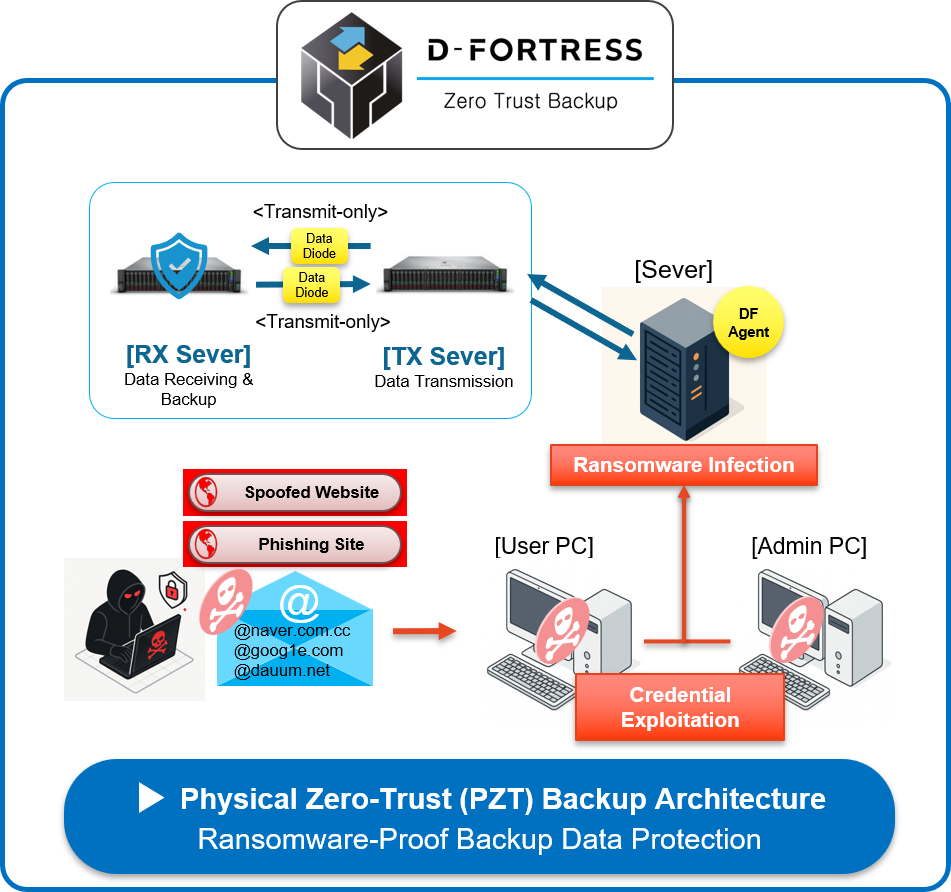
Illustrates the structure of the PZT-Vault backup system based on Physical Zero Trust (PZT).
D-FORTRESS guarantees 100% recovery, eliminating the need to pay ransoms to hackers and preventing business loss costs resulting from data loss.
Our AI engine continuously monitors backup data integrity in real-time and provides forensic analysis data on the ransomware infection time and intrusion path.
Beyond PZT, we establish multiple layers of defense, including In-Transit Data Encryption (chunk-based), network traffic analysis, and Zero Trust Network Access (ZTNA).
All backup scheduling, retention policies, and recovery tests can be managed intuitively from a single console, minimizing operational complexity.
Hackers target the weakest link. Check if your backup has achieved Physical Zero Trust independence.
Request a free, customized security assessment and find the optimal D-FORTRESS model for your company.
+82 70-8080-4910